Best Practices for Industrial IoT Security
As factories and industrial systems become increasingly connected, cybersecurity threats are on the rise. This article covers key Industrial IoT security best practices, including network segmentation, encryption, and secure remote access protocols, to help safeguard your automation systems from cyber risks.
The rapid growth of the Industrial Internet of Things (IIoT) is revolutionizing manufacturing and production processes. While IIoT offers unparalleled efficiency and connectivity, it also introduces complex cybersecurity challenges. In this article, we explore technical best practices for securing industrial IoT systems—from network segmentation to zero trust architectures—ensuring robust protection against emerging threats.
Industrial IoT security is not merely an IT concern; it’s a core element of operational technology (OT) that protects critical infrastructure and industrial control systems (ICS). With increasing connectivity among sensors, controllers, and enterprise networks, vulnerabilities have multiplied, exposing manufacturing lines, energy plants, and supply chain systems to cyberattacks. This guide provides a technical deep-dive into proven strategies for safeguarding your industrial environment.

Understanding the Threat Landscape
Industrial networks are attractive targets for cybercriminals due to the potential for disruption and financial damage. Key threats include:
- Unauthorized Access: Attackers may gain entry through weak authentication or unsecured endpoints.
- Malware and Ransomware: Infections can disrupt operations and compromise sensitive data.
- Data Breaches: Unencrypted communications or vulnerable interfaces may expose critical information.
- Physical Attacks: Tampering with devices on the plant floor can lead to system compromise.
Understanding these vulnerabilities is the first step in developing a comprehensive security strategy.
Best Practices for Securing Industrial IoT
1. Comprehensive Risk Assessment and Vulnerability Management
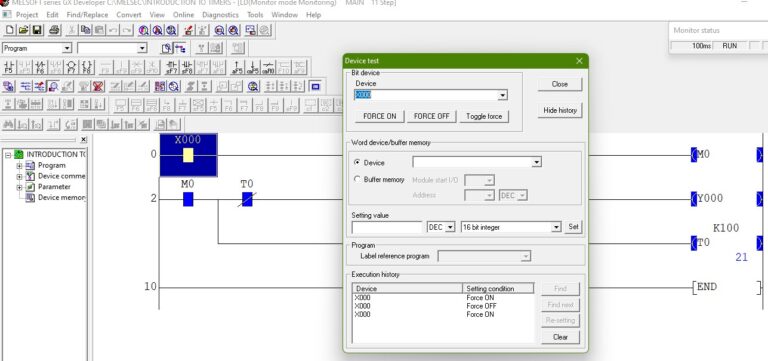
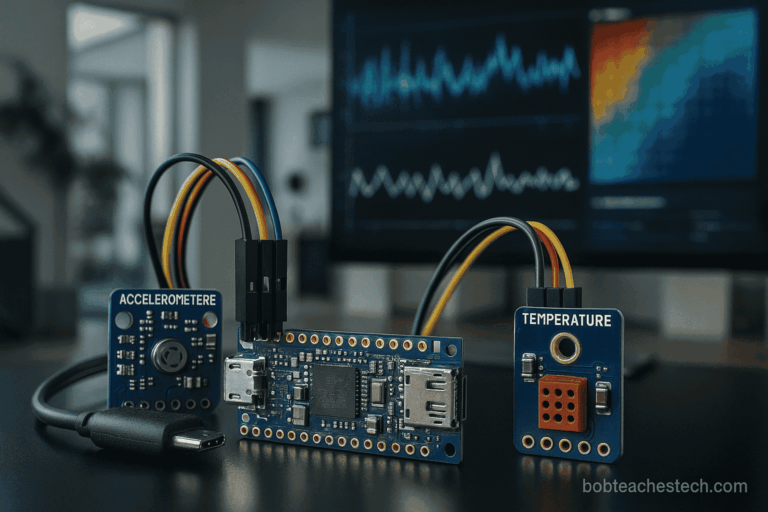
Perform regular risk assessments to identify vulnerabilities across your IIoT ecosystem. This involves mapping all connected devices—from sensors and actuators to PLCs and SCADA systems—and evaluating their potential impact on overall operations.
- Implement Vulnerability Scanning: Use automated tools to continuously scan devices and network segments.
- Penetration Testing: Periodically test security measures with controlled simulated attacks.
- Risk Prioritization: Focus on high-impact vulnerabilities that can compromise both safety and production.
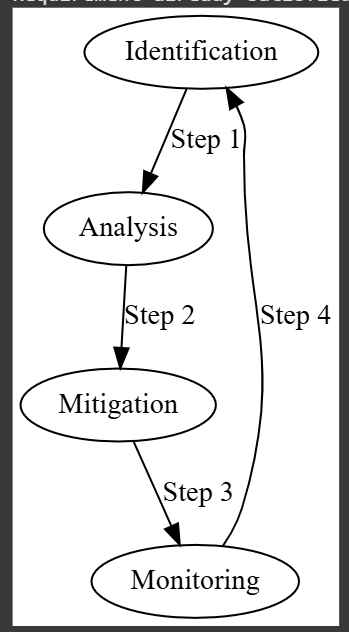
A risk assessment cycle that forms the foundation of IIoT security. Image used courtesy of Bob Odhiambo.
2. Network Segmentation and Isolation
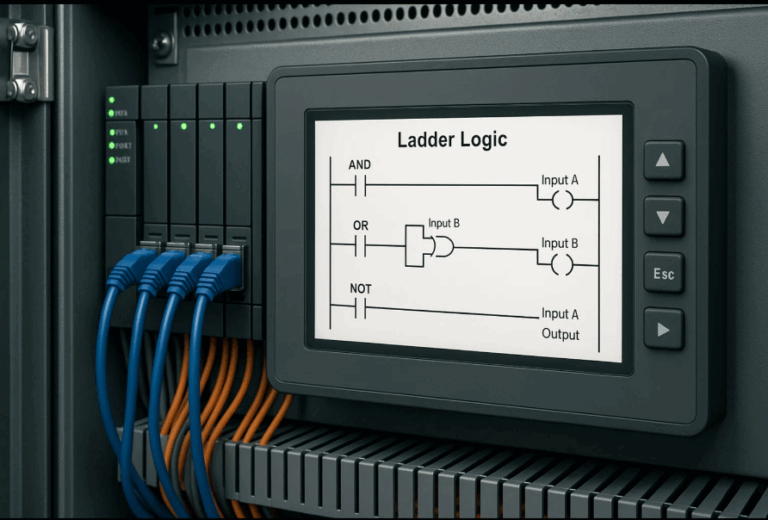
Segregate your network into zones to limit an attacker’s lateral movement. Network segmentation is especially crucial when integrating IT and OT environments.
- Separate Critical Systems: Isolate SCADA, PLCs, and other OT devices from the corporate network using firewalls and Virtual LANs (VLANs).
- Use DMZs for External Interfaces: Place any externally accessible devices in a demilitarized zone (DMZ) to provide an additional layer of protection.
- Micro-Segmentation: Implement micro-segmentation at the device level to further contain potential breaches.
Image Suggestion: A diagram showing a segmented industrial network with clearly defined IT, OT, and DMZ zones.
Image Caption: “Network segmentation minimizes risk by isolating critical IIoT components.”
3. Implement a Zero Trust Architecture
The traditional perimeter-based security model is no longer sufficient. Zero trust means that no device or user is inherently trusted—even those inside your network.
- Strong Authentication and Authorization: Use multifactor authentication (MFA) and role-based access control (RBAC) for all devices and users.
- Continuous Monitoring: Validate device and user behavior continuously rather than relying solely on initial authentication.
- Micro-Policies: Implement granular security policies that control access at the application and data level.
4. Secure Device Management
As the number of IIoT devices grows, so does the challenge of securing them. Effective device management should cover:
- Firmware Updates: Ensure all devices receive timely security patches and firmware updates through a secure update mechanism.
- Device Hardening: Disable unnecessary services, change default credentials, and configure devices to operate with the least privileges required.
- Asset Inventory: Maintain a comprehensive, up-to-date inventory of all connected devices for better monitoring and incident response.
5. Data Encryption and Secure Communication
Data exchanged between IIoT devices and central systems must be protected from interception.
- Use Strong Encryption: Employ AES-256 or similar encryption standards for both data in transit and at rest.
- Secure Protocols: Adopt secure communication protocols such as TLS for web-based interfaces and VPNs for remote access.
- Endpoint Security: Ensure that every endpoint, including legacy devices, supports secure communications through firmware upgrades or additional hardware security modules.
6. Continuous Monitoring and Anomaly Detection
Constant monitoring is essential to detect and respond to security incidents in real time.
- Security Information and Event Management (SIEM): Deploy SIEM solutions to collect, correlate, and analyze logs from all network segments.
- Intrusion Detection Systems (IDS): Use both network-based and host-based IDS to monitor traffic anomalies and potential breaches.
- Behavioral Analytics: Leverage machine learning to establish a baseline of normal activity and detect deviations that could indicate a compromise.
7. Develop an Incident Response Plan
Despite best efforts, breaches may occur. An effective incident response plan minimizes damage and reduces downtime.
- Define Roles and Responsibilities: Establish a clear chain of command and response procedures.
- Regular Drills: Conduct periodic simulation exercises and tabletop drills to ensure readiness.
- Post-Incident Analysis: Implement processes for post-incident reviews to identify lessons learned and improve defenses.
8. Secure Supply Chain and Vendor Management
Industrial IoT security extends beyond in-house measures to include external partners and vendors.
- Vendor Security Assessments: Evaluate vendors’ security practices before integrating their products.
- Contractual Obligations: Include security requirements and incident response obligations in vendor contracts.
- Third-Party Monitoring: Regularly audit third-party devices and services integrated into your IIoT network.
Emerging Trends and Future Considerations
As technology evolves, new approaches are emerging to further enhance IIoT security:
- Edge Computing Security: With more processing at the edge, securing edge devices becomes critical. Future strategies include distributed ledger technologies (blockchain) for tamper-proof logging.
- Artificial Intelligence in Security: Machine learning algorithms are increasingly used to predict and mitigate threats before they occur.
- Quantum-Safe Encryption: As quantum computing advances, planning for quantum-resistant encryption protocols will be essential.
Industrial IoT Security
Industrial IoT security is a multifaceted challenge that requires a comprehensive, layered approach. By conducting regular risk assessments, implementing robust network segmentation, adopting a zero trust model, securing device management, encrypting data, continuously monitoring systems, preparing an incident response plan, and managing supply chain risks, organizations can significantly enhance the security posture of their IIoT environments.
Adopting these best practices not only protects your industrial assets but also ensures operational continuity and safeguards against potentially catastrophic cyberattacks. As technology continues to advance, staying informed and proactive about emerging security trends will be key to maintaining a resilient and secure industrial network.
Implementing these strategies may require time and investment, but the long-term benefits include reduced downtime, improved operational safety, and a stronger defense against increasingly sophisticated cyber threats. Stay ahead by continuously reviewing and updating your security protocols in line with emerging trends and evolving risks.